CyberLock, Inc. is a supplier of “key-centric” access control systems dating back to 2000 when the first CyberLock branded locks and smart keys were introduced to the market by Videx. In 2013, CyberLock, Inc. was spun off as an independent company but maintains strong ties to Videx. The two companies continue to collaborate on future innovations.
VIDEX was originally based on their proprietary smart key and cylinder. The smart key had a unique shape and the “keyway” in the cylinder was distinctive. The cylinders could be fitted to conventional door hardware thereby enabling electronic access control using existing locks. No wiring and using existing hardware made for a unique solution.
The cylinders required no power to operate making them good choices for locations where power and communications might be unavailable. The smart key provided the power to operate the cylinder and also collected and distributed data, such as the activity log throughout the system.
The VIDEX product line has matured and grown and reflects the company’s focus on being applications oriented and providing solutions in response the requests of its dealers.
Typical VIDEX applications include:
- Airports
- Commercial Facilities
- Education
- Healthcare
- Public Safety
- Transportation
- Utilities
- Vending machines
- Worship Facilities
VIDEX can be integrated with other security products to provide unique yet totally supportable solutions for what seems to be unlimited special purpose high security applications.
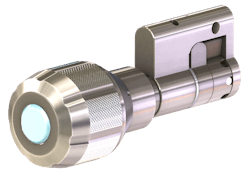
CyberLock is an innovative lock system that seamlessly converts existing mechanical locks into a full-featured access control system consisting of:
- CyberLock cylinders
- CyberKey smart keys
- Communication devices
- CyberAudit management software
- CyberLock Electromechanical Cylinders – High security electronic lock cylinders provide beyond-the-door capabilities.
Is CyberLock considered high security? CyberLock’s Sandra Yager comments: “In as it relates to the CyberLock access control system, we use the term "high security" in the literature you reviewed to allude to the relative amount of time and resources required to circumvent the system, as compared to alternative solutions such as mechanical cylinders. In particular, features of CyberLock that increase the time and/or resources required to circumvent the system include the presence of a restrictive keyway that prevents traditional methods of picking, the ability to manage and program keys to revoke access privileges, the ability to expire keys on a periodic basis, use of different key-types, lock cylinders that resist physical manipulation and destructive entry techniques, among others. Acknowledging that an infallible security system is unattainable, the principle objective of any effective security system is to make the cost of any attack greater than the possible payoff. The CyberLock system has consistently achieved this objective over the past 16 years in the field.”
BASICS: How Cyberlock works
Step 1. Replace existing mechanical cylinders with CyberLock cylinders.
Each CyberLock is an electronic version of a standard mechanical lock cylinder. Installation is as simple as removing the original cylinder and replacing it with a CyberLock cylinder. Installation requires no wiring or batteries, making installation quick and easy.
Step 2. Assign a CyberKey to a user.
Keys are programmed with access privileges for each user. A standard key holds a list of locks the user may open, with a schedule of days and times when access is allowed. For instance, the key can be programmed to allow access from 8 a.m. to 6 p.m. on weekdays and 10 a.m. to 4 p.m. on Saturdays. It can also be programmed to expire on a specific date at a specific time for increased security.
Step 3. Access locks.
When a CyberKey meets a CyberLock, the cylinder is energized and an information exchange occurs to determine if the key has access to that specific cylinder. The event and time is stored in both the lock and key. Lock cylinders and keys also record when an unauthorized attempt to open a lock occured.
Step 4. Download audit trails and update keys via Communicator devices.
Expiring keys regularly ensures users frequently update their keys. When validating keys, the system downloads the audit trail and uploads new access privileges to the key. An expired key will not work until it is updated.
Step 5. View audit trail.
The CyberLock system is managed centrally through CyberAudit software. Customized audit reports and automatic notifications on suspicious activities can be automatically generated via email.
Features include:
- Over 370 electromechanical cylinders have been designed for doors, cabinets, padlocks, containers, equipment, safes, and more.
- Cylinders retrofit into existing mechanical hardware.
- No wiring or battery required at the lock.
- Controlled access with audit trails provided even during power outages.
- The most recent 1100 access events are saved to cylinder memory.
- Efficiently packaged in highly durable fiberglass-reinforced cases.
- Power from key energizes cylinders.
- Rechargeable or replaceable battery options are available.
- Saves thousands of access events to key memory.
- Security Administrators may set expirations to minimize risk due to lost or stolen keys.
- Keys contain encrypted access codes that bind key to one system.
- Scheduling can range from standard to custom schedules.
- Keys cannot be duplicated.
Security
Unlike mechanical pin-based locks, CyberLock cylinders have a unique design that negates standard lock picking tools.
- Encrypted access codes bind cylinder to one system.
- Unchangeable unique ID within each cylinder cannot be duplicated.
- Multiple high-security options are available.
- CyberKey Programmable Smart Keys – Electronic keys store individual key holder access permissions.
Options
Having a variety of communicator options available allows organizations to create the right balance between convenience and security.
• IR Encoders and USB Stations connect directly to an available USB port.
• WebStations and CyberKey Authorizers connect over a network from remote locations without a computer.
• CyberKey Vaults store unprogrammed keys until programmed and released to an authorized user.
• Smartphones enable remote employees to update keys in the field.
• CyberAudit Software – Manages both the CyberLock, key-centric solution, and the hardwired Flex system simultaneously. CyberAudit software is available in two software packages: Enterprise Basic and Enterprise 8.0. Both software versions are categorized by the number of key holders and can manage thousands of users and locks.
Enterprise Basic: Enterprise Basic is an excellent choice for small-to-medium-sized companies that need key control and reporting. It brings a few of the essential features of Enterprise 8.0 in an easily manageable platform.
Enterprise 8.0: The full version of Enterprise 8.0 is a feature-rich management software, ideal for large, complex, and geographically widespread installations. Enterprise 8.0 offers all of the features of Enterprise Basic as well as advanced options like Bluetooth and Wifi CyberKeys, and the ability to share locks with other Enterprise 8.0 users.
Flex System
The Flex System enhances the CyberLock product line by adding the capability to control a variety of access control and security elements using both Flex System modules as well as third party access devices:
- Open a door
- Activate a light
- Sound an alarm
- Activate a camera
The Flex System is comprised of a variety of modules that can be mixed and matched to create a custom access control system. The modules are plugged into a Hub which is directly connected to CyberAudit management software.
The Flex System Hub connects with CyberAudit software and provides power to the Flex System modules. Embedded memory in the Hub stores access permissions and saves audit trail information, enabling continuous operation even when a network connection to the software is interrupted. Moreover, power outages can be mitigated by connecting a back-up battery or auxiliary power source directly to the Hub.
A variety of Flex System modules are available for a customized access control system:
• Input modules such as RFID readers and Keypad Displays can be used individually or combined for dual-credential door access.
• Weather resistant key vault modules can be installed in the field to securely store CyberKeys for convenient remote employee access.
• The multi-function Keyport module simultaneously activates electric door strikes and updates CyberKeys.
The Flex System Door & I/O Module
The Door & I/O module expands the capabilities of the Flex System even further. As a door controller, it provides power to an electric door strike and unlocks it when an approved key card is presented. It has additional inputs and outputs that can control relay devices such as alarms, speakers, cameras, or sensors. Finally, it can connect to compatible third party Wiegand devices such as HID readers and biometric scanners.p4
• Grant access via text or email
• Grant tempoary or ongoing access
• Works with any smartphone
• No app to download
• No Bluetooth to pair
• Infrared key fob is also available
FlashLock
FlashLock uses serial optical communications technology combined with any hand-held device with a web browser to issue and receive access to any lock retrofitted with the FlashLock system. There is no Bluetooth to pair and no app to download, saving battery life and making FlashLock compatible with any smart device. FlashLocks can be opened with a cellphone or tablet or by using an infrared key fob.
FlashLock is secure and easy to use. Anyone can receive temporary access or ongoing scheduled access via permissions sent by text or email.
Once users access the link, the screen of the hand-held device will flash.
This tells them they are allowed to access this FlashLock. They hold the phone to the lock and the lock will flash. Turn the lock and entry is granted. If customers want to adjust or remove permissions, there is a user-friendly, web-based interface to make those changes at any time.
FlashLock is is an ideal solution for residential or vacation homes, college dorms, apartments, hotels, churches, and more. FlashLock allows owners of residential facilities to control who enters what space at what time.
More info: www.cyberlock.com
About the Author
Tim O'Leary
Tim O'Leary is a security consultant, trainer and technician who has also been writing articles on all areas of locksmithing & physical security for many years.