Stand-Alones: Gateways to System Expansion
The term “stand-alone door control” is somewhat outdated given the recent meteoric developments in electronic access control.
Stand-alone door control systems initially were divided into:
- Mechanical solutions that used latching hardware and mechanical keypads or keys to control the locking and unlocking.
- Electronic solutions where the physical security was provided by mechanical locking hardware, electromechanical locking hardware (electric strikes), electromagnetic locking hardware (maglocks or shear locks), door operators, latch retractors, electrified exit devices or other hybrid devices. Control was by some type of electronic or electrical control. Traditionally, power for the electronics as well as the locking mechanism was wired into the door system.
Two examples of the Early Dark Ages are the mechanical Kaba Simplex Lock and the electronic Continental Instruments Cypher Lock.
The Simplex was — and still is — a chunky lock with a key-in-knob lever and a five-button mechanical keypad. It looks industrial and is robust and reliable.
The access code could be single button presses or button presses in pairs or three buttons, with a total of five presses in a combination, a minimum of three recommended. This yields a possible 2,162 combinations.
The Cypher Lock was comprised of a keypad and a control box. The control box plugged into line voltage, which powered the electronics and provided a power output to the locking mechanism.
The keypad mounted on the wall on the exterior side of the controlled door, and the control box mounted within the protected area in a location convenient to the door but preferably protected from tampering. Loss of power to the Cypher Lock rendered it inoperative, although versions of the Cypher Lock had battery backup, so loss of power didn’t prevent the unit from operating.
The Cypher Lock keypad had 10 discrete switches. The access code required four digits, and each digit could be used only once in the code. That’s 5,040 possible codes.
Modern Times
As you probably know, an access control system unlocks a door controlled by three criteria:
- The user’s credential(s). Initially, this was a properly encoded key. That evolved to a PIN code, a valid credential, an enabled smartphone and even biometric attributes, such as facial recognition, or a combination of these criteria.
- Proper authorization to the building, door or area, at the right time of day.
- User data that matches what’s stored in a database. This information is stored as a list of valid users, possibly a list of invalid users, and an activity log of when doors are accessed, and it includes when and where users are within the system.
In the early days, how the individual doors were programmed, how door activities were communicated to the database and where and how databases were managed were differentiators among systems and why some systems stood more alone than others. Some devices had only one valid code or credential and didn’t test or compare an entry attempt with a database. You either were admitted or you weren’t. Some devices stored user data and rules locally. Programming was at each door and used the unit keypad or a cable to connect to a programming tool or computer.
Going back to the Simplex and Cypher Lock, here were two different approaches to door control with the same desired outcome. Permutations of each are used, only because of the improved connectivity available to computers and security systems, rarely is a door control stand-alone any more. Doors are networked more frequently, and programming and database management are fast and efficient.
Within the scope of a large security management system, there will be a range of openings that have different security requirements. So, the ease and ability to deploy the required security management solution and fulfill the requirement to add on doors rather than tear down and start over is what it’s all about. The plethora of access control products makes it easier to accomplish a wider range of solutions than ever before. A single door system now can provide a gateway to expansion.
Following are a few examples.
SDC E70 Series locks
SDC stand-alone battery-powered locks are loaded with features typical of hardwired systems. The E70 Series can retrofit existing cylindrical (E75), mortise (E76) or exit bar (E77) door lock preps.
The locks are ANSI/BHMA Grade 1 certified and operate via four AA batteries. All are keypad programmable and allow for four- to six-digit PIN codes.
PS versions within each individual lock series allow for expandability beyond stand-alone use through SDC software, up to 1,000 doors each.
More info: https://sdcsecurity.com
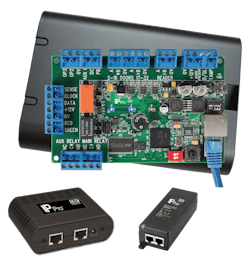
SDC IP Pro Series Controllers
SDC IP Pro Controllers allow for expansion from one stand-alone door up to a 100-door “Grid.” An additional Ethernet port allows IT departments to save a port when connecting an extra door at the server.
Every controller comes with secure, built-in software to manage up to 32 doors from any standard web browser to allow for real-time monitoring, user management and an audit trail up to 5,000 events. Or, you can download free PLUS software to control up to 100 doors from a single computer.
More info: https://sdcsecurity.com
Alarm Lock AirAccess
AirAccess takes Alarm Lock Trilogy Networx and ArchiTech Networx wireless locks and NetPanels, on existing and new installations, to a new real-time platform, combining intuitive cloud-based software and easily networked cellular communications that requires no client network, firewall or ISP access.
The new AirAccess App, which includes built-in free mobile credentials, provides an affordable hosted solution aimed at small and medium businesses, from a few doors and users to hundreds of each.
AirAccess is the first cell-based hosted access control system. It’s virtually wire-free from the cloud to the door, using Alarm Lock access technology plus cellular communications that make the network connections, independent from your customer’s networks, so there are no IT department or ISP issues.
AirAccess’ dependability is built in with a foundation of StarLink Cell Communications and Alarm Lock Trilogy Networx Access Control Locks and Panels that have standard Wiegand readers at the doors. You can mix or match.
Networx access locks, which feature global lockdown in seconds, eliminate door-to-door programming and audit trail event queries by communicating wirelessly via Ethernet or Wi-Fi. As with all Trilogy locks, the Networx are Grade 1 certified and provide years of long battery life for low maintenance and easy programming via their keypad, programmer or remote server.
Meanwhile, ArchiTech Networx Series locks feature the same durability and low maintenance but are customizable with hundreds of trims, finishes and reader designs.
AirAccess can provide installers with recurring monthly revenue from Alarm Lock Trilogy installations. Through AirAccess Cloud-based software, you’ll add real-time services to your installed base of all those lock accounts, while providing customers with a new app that includes mobile credentials, text alerts and emergency response from central station monitoring as an option.
More info: airaccesscontrol.com
Cansec Webster
Cansec knows that customers can change their mind at the flip of a switch: What they want today, they don’t want tomorrow and vice versa.
MAPMINI, MAP1 and MAP2 controllers that are provisioned with Webster firmware can create an expandable access control solution.
The controller works by plugging into a wired LAN connection and using the web browser on a computer or phone to set up and manage the system. There’s no software to install.
The MAPMINI controls a single door, the MAP1 two to four doors and the MAP2 two to eight doors.
If a customer outgrows their Webster unit, the Cansec Webster Trade-In Credit Program allows you to return the unit to receive a credit on your account, no matter when it was purchased.
If your customer grows beyond the eight-door max, Cansec can reprovision your Webster unit for use with Cansec’s First Access or CloudACS software, which can support up to 1,000 doors.
More info: www.cansec.com
Yale nexTouch
Yale nexTouch locks come in cylindrical, sectional mortise and exit trim configurations, and they can be upgraded easily from stand-alone use to connected systems because of their fully modular technology. Options include data on card and Zigbee or Z-Wave wireless for more-complex applications, including multifamily and small business.
Lock options and features include:
- A capacitive touchscreen or push-button keypad
- Privacy mode enabled by a button push
- Up to 500 user codes in keypad-only operation
- 9-volt battery backup prevents lockout even if the batteries fail
- Available in four finishes and three lever designs
The mortise and exit trim versions accept conventional, interchangeable-core and high-security cylinders, including those from manufacturers besides Yale parent ASSA ABLOY. The exit trim is compatible with exit devices from Corbin Russwin, Dorma, SARGENT and Von Duprin, among others.
More info: www.yalecommercial.com
dormakaba E-Plex series
dormakaba’s E-Plex series of locks creates a range of system options. E-Plex standard locks start as a stand-alone access solution for a single door. Programming solutions build the locks into an enterprise solution that can span multiple facilities and thousands of doors.
dormakaba’s free E-Plex software download can increase system control and expand the user’s lock management options. Versions include narrow-stile trim and deadbolt locks.
More info: www.dormakaba.com
Paxton PaxLock Pro
The PaxLock Pro can be stand-alone or as part of a networked solution, which provides a versatile access control solution that can grow with the demands of a site. The upgrade from stand-alone is simple.
The PaxLock Pro can be used as part of a Net2 access control system or used with Paxton10, access control and video management. Versions of the PaxLock Pro are compatible with standard cylindrical doors that use a tubular latch or mortise locks.
More info: www.paxton-access.com
Tim O’Leary is an experienced security consultant and a regular contributor to Locksmith Ledger.
About the Author
Tim O'Leary
Tim O'Leary is a security consultant, trainer and technician who has also been writing articles on all areas of locksmithing & physical security for many years.