Contrary to what you may have been told, IP does not necessarily mean “In for Problems.” IP is the acronym for Internet Protocol which is the set of techniques used by many hosts for transmitting data over the Internet. The current version of the Internet protocol is IPv4, which provides a 32-bit address system.
Internet protocol is a "best effort" system, meaning that no packet of information sent over it is assured to reach its destination in the same condition it was sent. Often other protocols are used in tandem with the Internet protocol for data that for one reason or another must have extremely high fidelity.
Every device connected to a network, be it a local area network (LAN) or the Internet, is given an Internet protocol number. This address is used to identify the device uniquely among all other devices connected to the extended network.
TCP/IP (Transmission Control Protocol/Internet Protocol) is the basic communication language or protocol of the Internet.
TCP/IP is a two-layer program. The higher layer, Transmission Control Protocol, manages the assembling of a message or file into smaller packets that are transmitted over the Internet and received by a TCP layer that reassembles the packets into the original message. The lower layer, Internet Protocol, handles the address part of each packet so that it gets to the right destination.
TCP/IP uses the client/server model of communication in which a computer user (client) requests and is provided a service (such as sending a Web page) by another computer (server) in the network. TCP/IP communication is primarily point-to-point, meaning each communication is from one point (or host computer) in the network to another point or host computer. TCP/IP and the higher-level applications that use it are collectively said to be "stateless" because each client request is considered a new request unrelated to any previous one (unlike ordinary phone conversations that require a dedicated connection for the call duration). Being stateless frees network paths so that everyone can use them continuously.
Most but not all TCP/IP uses Ethernet-based networks. Ethernet networks use the familiar RJ-45 connectors and Category cable.
There are four unshielded twisted pairs in a Category 5 cable. Currently Category 5e is the flavor of the day in networking, with Category 6 standing in the wings waiting to take center stage.
Security applications have different bandwidth requirements. Video requires high bandwidth, while access control typically will require far less.
Category 6 is rated for Gigabit network speeds. CAT 5 cable will support 10/100 Ethernet; also referred to as Ethernet and Fast Ethernet.
CAT 5e cable will support Ethernet, Fast Ethernet, and Gigabit Ethernet. It is completely backwards compatible, and can be used in any application in which you would normally use CAT 5 cable.
Cross talk is the electrical interference that results when one wire's signal effects another wire's signal.
CAT 5e cable provides a significant performance enhancement over Category 5 with respect to crosstalk.
Bandwidth is the information-carrying capacity of a system. The greater the bandwidth, the greater the information-carrying capacity in a given period of time.
CAT 5e cable is rated at 350 megahertz. This increased bandwidth (compared to CAT 5 cable) that allows it to support Gigabit Ethernet.
The slowest element in a network will throttle down the maximum bandwidth of the network, but the network must be designed to accommodate the fastest device connected to it, or performance will suffer, and your client will not be happy.
We all have experienced sluggish network performance which results in choppy video, or interruptions of downloads or opening of web pages.
In security applications, sluggish network performance can result in a disaster rather than just an annoyance.
IP technology has achieved a relatively high performance level and has found acceptance and has entrenched itself in security technology, so it is a necessity that security professionals have at least a working knowledge of it,
Besides being a protocol for data transmission, the term IP is also used to describe a variety of security components and techniques. Some of them are described below
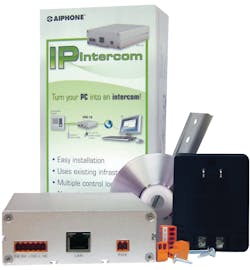
Aiphone
AIPHONE IPW-1A offers voice-quality Intercom function over standard IP based networks. Designed specifically to integrate seamlessly into a new or existing LAN / WAN infrastructure, the IPW-1A system is capable of supporting hundreds of stations. It provides intercom/paging solutions to a large variety of applications including commercial, industrial, residential, general security, office, and institutional. Each IPW-1A includes Aiphone’s “CommuniCenter” software for remote door release, group calling, event logging, and audio recording.
Features are:
- Cost-effective multi-master (PC-based) based design
- Compatible with IE Series sub stations and AX-DM
- Scalable to hundreds of stations / locations
- Works with standard wired and wireless network infrastructure. (LAN/WAN)
- Digital audio recording and playback capability via included software.
- Relay output for remote release (N/O or N/C)
- Up to 387’/(2 CONDUCTOR 22AWG); 980’/(2 CONDUCTOR 18AWG) between door station and IPW-1A
- One year warranty effective when device is deployed
Hardware Specifications are:
- Input Voltage: Use Aiphone PT-1211C (included); 15-24V AC/DC
- Network Interface: 10/100 Base-T Ethernet (Auto detection) RJ-45
- IP Assignment: Static or Dynamic
- Hardware Protocols: TCP/IP, UDP, DHCP, SNMP, AutoIP, SonicIP, Ipzator
- Transport Bandwidth:
≈128Kbps per active session (normal mode)
≈64Kbps per active session (low bandwidth mode)
- Audio Encoding: PCM (raw), G.7II ( Law)
- Audio Sampling: 16bit at 8kHz (normal mode) 8bit at 8kHz (low bandwidth mode)
- Output Level: Determined by sub station
- Relay Contact Rating: 30V AC/DC 1.0A (resistive)
- Operating temperature: 32°F to 104°F (0°C to 40°C)
- Dimensions: 1-1/2″H x 4-1/4″W x 4-15/16″D
Intelli-M®
The Intelli-M® eIDC Ethernet-enabled integrated door controller is among the first PoE access control system controllers and provides fully distributed intelligence for access control and alarm monitoring.
This Ethernet-enabled door controller is packed with powerful features that can fit in a small, compact two-gang box to control all peripheral door hardware. It is easy to install and program.
The Intelli-M eIDC controller operates autonomously with true peer-to-peer communication, independent of a network or PC workstation and is designed to minimize the impact of any component failure.
Connections to peripheral equipment can be verified on the spot using built-in line status indicators.
The Intelli-M eIDC controller can operate independently with its embedded Web server or with hundreds Intelli-M eIDC controllers through the server-based Intelli-M® Access security management software.
The Intelli-M controller uses external readers, so the controller can be located within the protected area, making for a higher level of security than with a reader using integral electronics.
The Intell-M supports multiple doors within a single site. This differentiates the Intelli-M form other products in this class.
Q&A: Wayne Jared, infinias
We contacted Wayne Jared, president of infinias, LLC, for some first hand info about this product. Following are Ledger’s questions and Jared’s answers.
How would you define the Intelli-M product category?
Intelli-M is an edge device solution. The controllers are designed to be installed out at the door and leverage corporate infrastructure. Access control devices are typically very low bandwidth and don’t introduce enough new load on the network to require upgrades.
What differentiates your product from others in this category?
From a hardware perspective, I would suggest we have the most capable device in this category. With three outputs (2-OC, 1-Relay), four inputs, support for two card readers and more, we have plenty of I/O available. We support 64,000 cards, 16,000 cached events, web mode for single door use, the ability to monitor a second or third door.
What motivates dealers to migrate towards your solution?
IT savvy dealers and integrators are looking for an easy to install, scalable and robust solution that leverages the IT infrastructure. These dealers are able to deploy Intelli-M at a lower cost per door than traditional access control system allowing each installation to be more profitable to them.
What is the typical deployment configuration?
PoE controllers are installed at the door and wired directly to the door components. They are then managed over the network by our browser-based software platform, Intelli-M Access.
When does it become advisable to use your software?
Anytime you want to manage multiple doors from your desktop and have a single cardholder database, using Intelli-M Access software makes sense and is a great value.
What is the warranty?
infinias hardware products come with a two-year warranty; the software comes with a one-year warranty.
How's your tech support?
Our tech support group is based in Indianapolis, IN, and provides phone support from 7:30 a.m.-6 p.m. Eastern standard time. We then have after hours support until 8 p.m. EST.
Intelli-M® eIDC Product Features include:
• PoE (Power over Ethernet) carries both data and power for the controller and peripheral door hardware
• Peer-to-Peer Communication keeps data flowing even if a server connection is interrupted
• 100% Distributed Intelligence
• Small Form Factor makes installation in tight spaces easy
• 3-State Alarm Monitoring for Normally Open, Normally Closed, and Trouble (either cut or short)
• Anti-Passback
• 16,000 Local Event Buffering
• 2 Reader Ports support proximity readers with or without keypads, or any logic device (such as an Egress Button or REX Device) that provides a combination of control of both entrance and exit for a single door
• Supports DHCP and Static IP addresses
• AES (Advanced Encryption Standard) 128-bit Encryption
• Embedded Web Server provides complete control of the device without the need for a server for stand-alone doors
• Integrated, Non-mechanical, Infrared Tamper Sensor for high reliability and precision
• Built-in Warning Buzzer provides a local alarm without requiring an external alarm device
TQ&A Alarm Lock’s Bob Swoope
Alarm Lock is a pioneer in standalone electronic access control. They recently introduced a wireless version of the Trilogy, and we contacted sales manager Bob Swoope for a product update.
How long has the PDL6100 (NETWORX) been out?
Networx went through five years of testing and development, including one year of in field Beta Testing prior to the April 2009 release to the market
How has it been received by dealers and end-users?
Extremely well, we have a much diversified list on end users with installed product. Especially popular are these three features: Schools and universities have been very keen on Networx’s systemwide 10-second global lockdown/unlock, activated from any lock or their network’s PC. Scores of hospital administrators noted they like the ability to Remotely Manage their systems, 24/7, via VPN-connection; and, all end users and locksmiths have been impressed by Networx exceptional, unsurpassed battery life, exceeding five years.
In which markets is it finding acceptance?
Virtually all markets where access is necessary and budgets are tight – that’s pretty much everywhere. However we’ve seen particularly strong acceptance in Healthcare, Education, Government, HOA, Property Management, Churches, Fire Department, Police Departments, Tele-Communication, Municipalities, Corporations, Industrial, Manufacturing to name a few.
Is it easy to deploy?
Extremely! The Trilogy Networx install very much like standard Trilogys and can operate as standalones until networking is done. Their Gateway simply plugs into the end user’s existing LAN or WAN and then the FREE DL Windows Software is loaded on a PC connected to the same LAN/Wan where both Trilogy Networx and original Trilogy locks share one common database. Another plus, Networx keeps both equipment and labor costs down—there are no repeaters -- No hardwiring to server; No extra power supplies, No access panels and up to 63 Networx locks and a PC communicate wirelessly, AES-encrypted thru a single 900MHz bidirectional gateway.
Is it compatible with XP, Vista and W7?
Yes
What equipment does the dealer require?
We carry a sales demo kit that literally takes five minutes to set up for presentations and demonstrations. Should a dealer want a demo kit, they can purchase a kit from their Networx Distributor for $1,000 net cost. This provides them a complete selling kit, Prox/PIN PDL6100, Gateway and Router mounted on a demo board and carry case. All they need as a laptop.
What hardware must the end-user provide?
An existing LAN or WAN; and PC.
Trilogy Networx™
Trilogy Networx™ Locks communicate wirelessly over any size network. They eliminate having to go to each unit for programming and audit trail retrieval by communicating wirelessly via Ethernet or 802.11B/G.
All original Trilogy standalone lock functionality is retained.
Networx provides a quick, easy, economical access system with advanced features & functions, like automatic schedules, event logs and support for 2000 doors and 5000 existing Prox. ID Cards/Badges, but with no wires to run, and no access panels or power supplies to buy or install.
Networx is Grade 1 durable wireless lock which can be installed in about an hour that communicates to a single Gateway. Each gateway can control up to 63 locks. The Trilogies can be networked to any non-dedicated Windows-based PC.
In addition to Wireless Trilogy Networx’ extended battery-life, (exceeding five years), Networx locks feature new network-wide capabilities, which can be executed from any lock on the network or from the network’s PC. This command set includes emergency priority global lockdown or unlock (deployed in seconds), and you can activate (non-priority) system-wide ‘free-passage’ or locking modes from the PC.
The new Trilogy Networx locks can seamlessly share one common database with existing legacy Trilogy locks hosted on free Alarm Lock DL-WINDOWS software.
Trilogy Networx™ features include:
- Locks support 802.11 or Ethernet
- Interface: Ethernet 10Base-T or 100Base-TX (using RJ45 Jack)
- Protocols: TCP/IP, UDP/IP, DHCP
- 802.11 Wireless Specifications
- WIRELESS STANDARDS: IEEE 802.11b; 802.11g
- FREQUENCY RANGE: 2.412 - 2.484 GHz
- OUTPUT POWER: 14 dBm + 1.5 dBm/-1.0 dBm
- MAXIMUM RECEIVE LEVEL: -10dBm (with PER < 8%)
- DATA RATES WITH AUTOMATIC FALLBACK: 54Mbps - 1Mbps
- RANGE: Up to 328 feet indoors
- MODULATION TECHNIQUES: OFDM, DSSS, CCK, DQPSK, DBPSK, 64 QAM, 16 QAM
- INTERFACE: Wireless 802.11b, 802.11g and 10/100 Ethernet
- PROTOCOLS: TCP/IP, UDP/IP, DHCP
For More Information
For more information on the products mentioned in this article, contact or local locksmith distributor or the following manufacturers.
Aiphone, 1700 130th Ave NE, Bellevue, WA 98005. Phone: 800-692-0200. Web site: www.aiphone.com
Infinias, 857 West Carmel Drive, Carmel, IN 46032-5804. Phone: 866.496.5783. Web site: www.infinias.com.
Alarm Lock, 345 Bayview Ave., Amityville, NY 11701. PhoneL 800-252-5625. Web Site: www.alarmlock.com.
About the Author
Tim O'Leary
Tim O'Leary is a security consultant, trainer and technician who has also been writing articles on all areas of locksmithing & physical security for many years.