Putting Your Finger On the Pulse of Access Control
When biometrics was introduced to the security industry, people scoffed at the idea of using parts of their bodies to gain access to a secured area. They had concerns about their voices being analyzed, their hands being radiated and their eyes being damaged by 'lasers.'
Voice recognition, hand geometry, and iris scanning all eventually moved into the role of acceptable means of identification for the security professional. The exception to the biometric scare was fingerprints. People have had their fingerprints recorded since birth.
Among all the biometric techniques, fingerprint-based identification is the oldest method. It has been successfully used in a variety of law enforcement and security applications. Large volumes of fingerprints are collected and stored everyday in applications including forensics, access control, and driver license registration. An automatic recognition of people based on fingerprints requires that the input fingerprint be matched with a large number of fingerprints in a database (FBI database contains approximately 70 million fingerprints!).
Professionals have come to the conclusion that everyone has unique, identifiable fingerprints. A fingerprint is made of a series of ridges and valleys on the outermost layer of skin of the finger. The pattern of ridges and valleys, as well as a variety of intersecting and ending points, determines the uniqueness of a fingerprint.
Fingerprint readers use algorithms as a method to identify and categorize. An algorithm is described as a step-by-step problem-solving procedure, especially an established, recursive computational procedure for solving a problem in a finite number of steps. To reduce the search time and computational complexity, it is desirable to classify these fingerprints in an accurate and consistent manner so that the input fingerprint is required to be matched only with a subset of the fingerprints in the database.
To map an entire fingerprint is time-consuming; even the most expensive equipment can take one or more minutes. Once the fingerprint is mapped, it must be compared to the database of fingerprints. This takes even more time. This is a significant amount of time when reading a fingerprint is used to control access.
For this reason, fingerprinting equipment manufacturers are constantly investigating methods to pool evidence from various matching techniques to increase speed and overall accuracy of their systems. A commercial fingerprint-based authentication system requires a very low False Reject Rate (FRR) for a given False Accept Rate (FAR). This is difficult to achieve with any one technique. In a real application, the sensor, the acquisition system and the variation in performance of the system over time is very critical.
One method of sub-classification is to require another means of credential along with the fingerprint. By utilizing a pin number, proximity card or similar method, authorized users can be authenticated more quickly because only one fingerprint must be compared to the fingerprint wanting access.
Following are three examples of fingerprint use as a means of identification with different types of security products. We'll examine a fingerprint reader used as a switch, a standalone lock that uses a fingerprint instead of a keypad and a security case opened by a fingerprint reader. Each item is from a different manufacturer and the details are included to receive additional information.
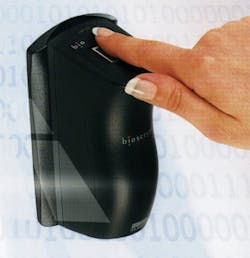
BIOSCRYPT V-SERIES READERS
Bioscrypt Inc. offers a line of fingerprint readers that are used as controls for electric strikes, magnetic locks or almost any access control product. The V-Flex, V-Prox and V-Pass fingerprint readers are a convenient way to provide facility security and positive user identification. Each model is designed to augment existing security infrastructures such as proximity, magnetic stripe, keypad/PIN and barcode readers.
The V-Pass model is an automatic one-touch fingerprint identification reader for up to 200 users. It has pigtail wire connections for RS 232, RS 485 and Weigand In/Out. Enrollment time is less than 3 seconds and verification time is less than 1 second (for a 100 user database). It has a False Acceptance Rate (FAR) of 0.20 percent and a False Rejection Rate (FRR) of 1 percent. Template size is up to 2400 bytes. Acceptable voltage is 7VDC to 24VDC.
The V-Flex model is a fingerprint identification reader used in conjunction with existing Weigand-based readers. It will enroll up to 4,000 users. It has pigtail wire connections for RS 232, RS 485 and Weigand In/Out. Enrollment time is less than 3 seconds and verification time is less than 1 second. Its FAR is 0.1 percent and its FRR is 0.1 percent. Template size is up to 350 bytes. Acceptable voltage is 7VDC to 24VDC.
The V-Prox model combines a self-contained fingerprint module with an HID proximity reader in one package. It will also enroll up to 4000 users and has pigtail wire connections for RS 232, RS 485 and Weigand In/Out. Enrollment time is less than 3 seconds and verification time is less than 1 second. Its FAR is 0.1 percent and the FRR is 0.1 percent. Template size is up to 350 bytes. Acceptable voltage is 7VDC to 24VDC.
VeriAdmin software is included free of charge and offers simple fingerprint template enrollment and administration. Flexible communication options support Weigand formats up to 64 bits. A duress finger option is available.
All three Bioscrypt models can be mounted on a flat surface, in a single gang or on a mullion. A trim plate is included to cover a single gang box. In addition, an outdoor enclosure is available.
Bioscrypt also offers the V-Smart, a two-in-one reader that combines the fingerprint technology with support for smart cards. With the V-Smart system, the fingerprint templates are stored on the smart card.
For more information on Bioscrypt Inc. go to www.bioscrypt.com
IST ISTEKI B-I/O SECURITY CASE
Isteki's B-I/O Security Case is a biometric firearm storage device. Its exterior dimensions are 12" long by 7-1/2" wide by 4-3/4" high. Approved by the State of California Department of Justice, the Security Case uses advanced fingerprint technology to authenticate wet, dry or oily fingerprints. Touching an enrolled finger to the pressure-based sensor activates the locking mechanism and unlocks within two seconds. There are no combinations, codes or sequences to remember. Up to three users can be enrolled.
Two nine-volt batteries supply the power for the reader. It comes with a low-battery warning signal and an auxiliary battery connector is built into the exterior of the aluminum alloy case.
A security cable lock port and a shoulder strap attachment link are included. Optional steel bolt-down plates are available. A high-security lock mechanism is for emergency over-ride opening.
For more information on IST Electronics, visit the web site www.isteki.com
HERALD DATANETICS HFD SERIES PRODUCTS
Herald Datanetics offers a variety of biometric fingerprint-activated products for home and small business applications. The HFD101S is a battery operated standalone lock for residential applications. The lock can be set to operate in one of three modes: Normal mode, Free Ingess mode or User Restriction mode. No programming is needed for this residential model. The HFD101S utilizes basic fingerprint management and will hold up to 99 fingerprint templates. This capacity is broken down into five master templates and 47 user templates with two fingerprints per user. Identification time is less than 1 second and the unlatch time is about 2.5 seconds.
The HFD112S is a battery operated standalone lock designed for small business applications. The lock can be set to operate in one of three modes: Normal, Free Ingess or User Restriction. In addition, the unit offers timed free ingress, timed restriction with 20 programmable time zones, a real-time clock and an events log memory with storage of the last 8,192 records. Programming is accomplished with the HFP110 programming kit.
This unit utilizes advanced fingerprint management and will hold up to 105 fingerprint templates. This capacity is broken down into five master templates and 50 user templates with two fingerprints per user or 100 user templates with one fingerprint per user. Identification time is less than 1 second and total unlatch time is about 2.5 seconds.
Four AA alkaline batteries supply power the Herald Datanetics units. The HFD101S has a battery life of 7,000 cycles and the HFD112S is rated at 5,000 cycles. An external DC power supply can also be used in place of batteries.
Available finishes include Polished Brass, Antique Brass, Satin Gold, Satin Chromium and Satin Nickel. Units are handed and available with a straight or curved handle style and a 2-3/8" or 2-3/4" backset.
Herald Datanetics also offers the HFA200S, a wall-mounted access control unit that can work in standalone mode or be integrated into an existing smart card, magnetic stripe, PIN code or time recording system.
For more information on Herald Datanetics Limited, go to www.heraldgroup.com.hk
CONCLUSION
In addition to the items referenced above, there are a variety of fingerprint reader products in today's market such as the Cansec Zodiac Lite, the Marks IQB, and the Recognition Systems' FingerKey.
Every security option you can become familiarized with will increase your ability to resolve your customer's security dilemma. Learn about as many new products as you are able to. Read the security industry trade magazines on a regular basis and attend trade shows and seminars to further your knowledge.