The possession of materials that pertain to the customer’s key control can create discord between the customer and the locksmith, especially when those resources are necessary to generate the combination of the keys.
Many customers whose business plan requires the management of a large keying system prefer to bring the expertise in-house, or alternatively delegate the management to entities (like national service providers) that in turn, manage locksmiths.
When surveyed as to why, many large scale customers cite the following issues:
1. There is little standardization when it comes to interpreting the means to generate key combinations. Locksmiths tend to develop then maintain the means to generate keys based on personalized techniques or non-standardized practices.
2. Sometime during the process of integrating records into a single database, locksmiths are asked to produce key control records pertaining to keying projects that they have participated in. Most of the time locksmiths are reluctant, not capable or directly refuse to comply with the request. The customer begins to wonder if that key records and materials privy to the customer’s keying systems are being held “hostage.”
3. When the customer requests information from the locksmith relating to the key combinations, the customer is “hit up” with an unexpected surcharge. This is perceived by the customer as an encumbrance or lien created by the locksmith.
4. There is no advantage in letting the local or regional locksmith manage these crucial records as the outcome are usually inconsistent and result in non-compatible data collection.
From locksmith’s perception, there is a lot of time invested in creating then maintaining keying systems, as the customer was never initially charged for this time. The locksmith considers the means of generating key combinations more as a tool that the locksmith purchased to develop the product (key combinations) that the customer purchased. To the locksmith, giving up the means of generating key combinations is tantamount to relinquishing control, which then leads to the dissolution of the relationship with the customer.
Many locksmiths demand exclusivity to the means of generating key combinations for the following reasons:
1. The level of system integrity can only be maintained when a single vendor provides all keying services.
2. Master key schematics are uniquely developed by the originator with the originator being the best source for additional expansion.
3. The means of generating key combinations may be proprietary to the locksmith. Separating the customer’s key records and the locksmith’s proprietary methods may be impossible to do. Turning over the system may result in exposure to the original design.
4. The process of generating key combinations and the maintenance of key control records represents a significant amount of time invested that the customer was never made privy to nor asked to pay for. In most instances, customers do not ask for key generation materials. Therefore, if the customer wants the key generation materials, the locksmith should at least be compensated for the time and knowledge invested.
Some customers consider generating key combinations as a mere sequential development of a matrix of numbers and cannot understand the locksmith’s reluctance to surrendering it. Some locksmiths consider surrendering the key generation resource like a chef giving up a prized recipe.
Locksmith Liability
I often consult with customers that have large keying systems.
Many times these customers are left in a quandary when dealing with an uncooperative locksmith who is refusing to relinquish key control records, especially the means to generate key combinations. The decision to acquire the records can range from the customer’s desire to integrate data to deciding to terminate a vendor’s services.
Part of my process is: to first try to act as a liaison between locksmith and customer, then possibly broker a deal.
When negotiations are deadlocked, I default to representing the customer as the point of contention always involves the customer’s property: keys; cores; and lock cylinders, and the customer’s right to maintain it.
The customer’s right to maintain the system is undisputed, providing prior agreements are not in effect.
The alternative to brokering is reverse-engineering the system and its components. It is surprisingly easy to do this and yields the following results:
The means of generating key combinations is rediscovered and secured for the customer.
Key control records are delivered to the customer in a format that is easier for the customer to understand and assimilate into a singular database.
In the process, all services performed by the locksmith are inspected. Any applied negligence is exposed; deviations from normal keying procedures are reported.
The locksmith can be held liable for all expenses relating to the effort.
Locksmiths intending on exclusive possession of key control records or the means of generating key combinations, should state this initially and in writing within the contract. This way, it is clear who owns what. Locksmiths who establish maintenance guidelines prior to performing services are in the driver’s seat.
What is the means to generate key combinations?
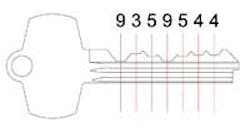
The actual cuts or combination of a key is called the key bitting. A list of all key combinations and key references is called a bitting list. (Figure 1) A matrix of numbers that displays all possible key combinations in a keying system is called a key bitting array. (Figure 2) A bitting list or key bitting array is a means of generating key combinations.
During new construction projects, lock or hardware companies will furnish bitting lists to architect or the customer’s agent. (Figure 3 - view in PDF format) Usually, when more key combinations are needed due to expansion or rekeying, the bitting list can be acquired through the architect or customer’s agent.
When locksmiths are asked to perform rekeying services, they may use bitting lists provided by lock companies or they may use alternative means of generating key combinations. Alternative means are:
- Proprietary software applications that automatically generate bitting lists while maintaining records of key issuance and lock cylinder assignments.
- Spreadsheets that derive specific key bitting information based upon a key bitting array.
- Bitting lists created by the hand of the locksmith.
- Bitting lists provided by other locksmiths for locksmiths.
Key Records
At the heart of any means to generate key combinations is the key bitting array. Once a group of locks have been keyed to a specific key bitting array, all expansion relating to the system must comply with the parameters included the same key bitting array. By itself the key bitting array cannot reveal how a specific key is cut or a lock cylinder is to be keyed.
Records that identify which key combinations were used to develop keys and build lock cylinders are basic key records. Key records can also include who was issued keys and where lock cylinders were installed.
Sometimes a locksmith will turn over the key records but not the key generating resource. This lets the customer know how locks are rekeyed but doesn’t include how to cut more keys or create new key combinations.
How to recover the cost of time invested
The locksmith who bids on a large keying project faces a lot of competition. Usually the job comes down to charging for service calls, lock cylinders and keys: by the unit, so much for the rekey of a lock cylinder; so much for key cut or originated. This allows the customer to compare apples-to-apples when it comes to deciding who shall be awarded the job.
The time invested in developing a bitting list and basic key records is usually wrapped into the flat-rate cost of rekeying a lock cylinder.
During the process of competing, the locksmith will lower the basic unit cost of rekey of a lock cylinder, which has the effect of discounting the time invested in developing bitting lists.
While a customer can be confused when odd charges appear on the initial estimate, the customer is very familiar with certain kinds of charges.
Instead of referring to a charge as “Developing the bitting list” or “Entering key records,” use “Administrative preparation.” Include the amount of hours and the rate relating to this charge.
Another recovery tactic is to include a statement that offers many options as to how the customer can take possession of the key control materials. When the locksmith includes this type of documentation in the estimate, the customer has to ask why the other bidders have not.
The following is a statement that makes the locksmith’s position clear when it comes to the handling of key generating resources and key control records:
“The described keying services rely on a unique list of keying combinations referred to as a bitting list. The locksmith has invested ______ hours at $________ per hours of administrative time to develop a bitting list and basic key records. These key control records reside with the locksmith so that the keying system can be properly maintained.
At a later date, the possession of these records can be transferred to the customer for this amount: $_________”
Caveats
A better means to convey the message is to include it in a list of caveats that include general information that customers need to know.
Here is a list of caveats that are informative to customers while conveying who owns the key control materials:
1. While incidents are rare, lock cylinders or cores that are master keyed can be attacked, resulting in the unauthorized origination of the Top Master Key (the highest master key in the system). The only known prevention from such an attack is the conversion of lock cylinders or cores to those that feature patented-controlled key stock. This type of key stock is not readily available to unauthorized sources. This prevention remains effective during the life of the patent.
2. The customer is aware of the above and has elected not to convert existing lock cylinders or cores to those that feature patented-controlled key stock.
3. Sometimes lock cylinders or cores have been altered with a file in an attempt to make keys work smoothly. When this occurs, replacement is necessary to prevent unintentional access with other keys. The locksmith will notify the customer when this occurs and reveal any additional charges associated with the replacement.
4. Rekey services have been requested. Part of that service is to account for existing keys and develop a system that limits as much as possible existing keys being operational in the new system. This is not always possible, as the locksmith may not have access to all existing keys or keys from a pre-existing system.
5. The development of an organization of change keys and master keys and other key control records is derived using the locksmith’s proprietary means of generating key combinations. The customer has not been charged for this resource, as it is strictly owned by the locksmith. After the project is completed, all key control records will be retained by the locksmith with all rights reserved.
6. The organization of change keys and master keys is pre-planned including future expansion that is sometimes necessary. If another locksmith is asked to expand the organization or create additional key combinations without consulting the original system, all warranties regarding the integrity of the key organization are voided.
Another method to bring harmony is to provide a minimum amount of materials that will suffice as key control records should the customer request them.
The abbreviated package includes the bare minimum:
1. A unique key bitting array. The bitting array needs to include the key combination of the Top Master Key, all possible key combinations that could be derived to create change or operation keys, the key combination to the control key if interchangeable cores are used, and the sequence of progression.
2. A table of key issuance information that includes columns referring to: the key reference; the key bitting, and who received the key.
3. A table of pinning information that includes columns referring to: a cylinder reference; and all the pins included in the cylinder or core.
Explaining how key references are associated with key combinations does not have to be included in this minimum package.
More detailed records can be kept with the locksmith, but the above abbreviated package will at least keep the locksmith clear of liability.
The Best Method
Bill your work appropriately, reflecting the true amount of time spent with these types of administrative tasks. In this manner, if and when the customer asks for the records, they can be easily handed over knowing the time invested was paid for.
In Summary
There are few reasons why a customer wants to keep the key control records.
Sometimes it is to integrate the key records into a computerized system in order to better manage the building space and the affected individuals. Other times it is to supplant the locksmith.
In either case it should be the locksmith’s goal to “lock” customers in by demonstrating superior performance.
In the case of computer integration, the locksmith that works with the company regarding the transfer of records will continue to be used by the customer to perform the keying services.
The supplanting of the locksmith is usually for cause. The superior performing locksmith does not have to worry about this.
The customer always has the right to determine who performs the keying services unless agreed upon during the contract negotiations.
Locksmiths should always turn over all key control records unless a prior agreement is in place that clearly states the locksmith’s intentions.