The Use of Biometric Technology in Security
The use of biometric technology for access control has gained acceptance in the industry and by the public for applications where verification of identity or authentication is required.
Security industry surveys report that about 75 percent of those polled currently use biometrics or plan to use biometrics in the future.
The fact that multiple factor authentications has been mandated by the Federal Government’s Department of Homeland Security essentially guarantees that biometrics will soon become the mainstay of identity verification in more and more civilian applications.
Automated identity verification has rapidly evolved since the inception of electronic access control. Keys and early mechanical single-code devices came first; however the identity of the key holder or code user could not be verified. Additionally keys could be lost or duplicated, memorized keypad codes could be shared, and the overhead associated with traditional keyed locks and the difficulty in achieving comprehensive and high levels of security management fostered the development of better solutions.
Next, encoded credentials and proprietary keyways were introduced. Each credential had unique encoding and the keys were difficult to duplicate without authorization. The credentials themselves used proprietary construction and formatting which made counterfeiting no longer a big concern. Encoded cards using magstripe, proximity and Weigand technologies. are well established and will continue to be the mainstays in access control.
However even with an encoded credential and a unique P.I.N. (Personal Identification Number, the identity of the individual in possession of the credential and code still was not guaranteed.
Herein lies the value of biometric technology in automated identity management. The operative word here is ‘automated.’ In situations where live security personnel are used, such as airports, your identity will be verified by the traditional method of having you remove your shoes, coat, belt, wristwatch, loose change, jacket, pacemaker; and you are carefully compared to a state or federally issued hologram imbedded, hermetically sealed photo ID. It’s a pretty good system, but it will be better with multiple factor authentication.
BIOMETRICS: WHAT IS IT?
“Biometrics” is the utilization of unique physical characteristics to verify the identity of people. Fingerprints, faces, veins, voices, and retina and iris patterns all have unique characteristics that can be quantified and stored digitally. Once a person’s unique attributes are converted into a digital template, that template can be stored and later retrieved to verify the person’s identity.
Unlike keys, PIN numbers, picture IDs, magnetic swipe and “smart” cards, biometric-derived identities cannot be transferred to another person, stolen, copied or counterfeited. Therefore, the application of biometric technology greatly reduces or eliminates the opportunity for identity theft and its consequences for the safety and security of individuals, organizations and even countries.
MEASURING MAN
The attributes of fingerprints, hands, veins, voices, faces, irises, retinas and even signatures and keystrokes all lend themselves to being measured, digitized, stored, retrieved and matched in order to verify someone’s identity. They have varying degrees of reliability and applicability, depending on the application; costs to implement; technology limitations and site variables such as: lighting, noise, weather, stress and other factors. The following are among the advantages of biometrics.
RELIABILITY: Improved technology results in fewer hardware failures and security lapses. Reader throughput rivals keypad and credential based system speeds.
CONVENIENCE: Newer biometrics are less intimidating than earlier efforts, with less body contact, no laser beams in the eye and no hygiene issues. This makes the biometric interface more user-friendly.
PRICE: The cost of the hardware and the amount of technical support required to keep biometrics have dropped, thereby making the technology more feasible.
EASE OF DEPLOYMENT: Biometric systems and readers are more robust and modular; software is written to interface more readily, and the readers are designed to withstand harsh environments.
SECURITY: Our society needs the most reliable foolproof methods of identity verification it can get, and biometrics meets these requirements.
Their usefulness also depends on how much the subjects who will be required to use the system are willing to cooperate. Here is a rundown on the various types of biometric identification.
Facial recognition. This one is a non-contact technique whose technology is rapidly coming of age as video analytics and IP gain control of the realm of CCTV video.
Iris recognition is one of the most accurate biometrics currently available, but requires physical contact between the subject and the reader appliance which many find objectionable; and uses a light source which many fear will damage their vision.
Retina recognition has a high degree of precision, but is considered one of the more intrusive biometric technologies.
Hand recognition has achieved a high deployment in biometric applications and achieves high performance levels because it can measure various features of the hand in order to develop a template.
Vein recognition systems are not readily available yet, but offer a level of precision similar to iris recognition technology.
Voice, signature and keystroke reliability depend on the subject’s stress level, ambient noise level, illness, etc., and also are more vulnerable to defeat.
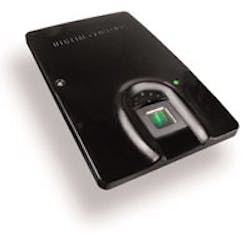
Fingerprint recognition is the most widely deployed biometric identifier because it is reliable and easy to deploy.
BIOMETRIC APPLICATIONS
Physical access control – Biometric identification can help separate the authorized from the unauthorized and make certain that only the “right” people come through the door – or go out.
Network security and electronic transactions – Identity thieves can gain unauthorized access to valuable information and/or financial resources, causing identity theft to become a pervasive and vexing problem. Biometric identification can prevent unauthorized access to computer networks and the information they contain.
Tracking time, attendance and materials – Biometric identification minimizes the mistakes and fraud when checking in, punching a time clock and making the rounds. Biometrics can help maintain the “chain of custody” for handling evidence and other sensitive or classified materials.
FIPS-201
In August of 2004, President Bush signed a 724-word document titled HSPD-12 which put forth the idea of an inter-agency which would recognize and secure a reliable form of identification to control physical access in federal facilities, and logical access to federally controlled information systems. Within six months, the original two-page directive proliferated into hundreds of pages of instructions all based on a new standard called the Federal Information Processing Standard 201, Personal Identity Verification of Federal Employees and Contractors (FIPS-201).
Among its stipulations is the requirement for a biometric component in each card. In addition to a photograph, templates of two fingerprints must be used when the card is presented to a biometric-enabled card reader, and the user punches in a P.I.N. This scheme provides three factor authentication: requiring something the individual has (the credential); something the individual knows (the P.I.N.); and something that is part of him (a fingerprint).
The technology is reaching out to include more applications than ever before. These include:
Prison Visitor Systems: Verifying prisoners and visitors so that identities cannot be switched and escapes effected.
Drivers’ Licenses: Eliminates licensing abuses especially among commercial drivers.
Vendor cards: For meal and related expenses on campus; streamlines billing and stops abuses.
Border Control: A growing concern, qualified travelers are expedited through checkpoints.
Voter Registration: Eliminates issues relating to ‘proxy’ voting and resulting disputes.
Benefit Payments: Huge savings as a result of welfare abuse by means of positive identification of beneficiaries.
Time & Attendance and Payroll Processing: Dramatic increases in efficiency and decreases in losses through automated identity verification.
Workstation and Network Access: A proliferation of inexpensive finger scan devices used to provide access.
Biometric Template
The biometric template is sample of the user which will form the basis of identification or authentication.
Biometric devices perform either identification or authentication roles. For large populations of users, the size of the database and the time required for a reader or a system to compare the live scan with the ones on file can prove problematical for several reasons.
One reason is that added comparisons increase the possibility of a False Positive (unauthorized scan is mistaken for an authorized one); or False Negative (an authorized scan is rejected).
Another is the amount of time it takes for the comparisons to be processed. Finally, the size of the database may make it impractical for local storage and mandate that readers be connected to networks and stored in centrally located storage devices or servers.
Authentication, as in the FIPS-201 standard, requires that the template be conveyed on the credential and when the finger or other body part presented to the reader, that a relatively quick 1 to 1 comparison occur at the terminal. The weakness of this system is that templates may not be archived and therefore a central record of all templates may not exist. While this might be observes as a preservation of individual privacy, the loss of the template may require that the individual submit to the creation of a new template, and the lost template could be used in some way to compromise the security management system.
Biometrics are suitable for all automatic identity management purposes, and will assume a more important role in security as time goes on.
McDonald’s Reduces Payroll Costs with Biometric HandPunches
Eighty-five McDonald’s restaurants are cutting payroll costs by up to 22 percent annually after incorporating the company’s Ingersoll Rand Recognition Systems’ biometric HandPunch biometric terminals to record time and attendance. The HandPunch terminal eliminates expenses associated with employee badges and fraud caused by buddy punching. Over 3,400 employees at 85 McDonald’s restaurants in Venezuela have been enrolled with the HandPunch over the past four years. On average, the system generates over 7,500 transactions each day resulting in over 2.5 million “punches” annually.
“McDonald’s moved to biometrics because they wanted to verify that the employee clocking in was really that person,” says Jose Ramon Casal of Caracas-based Electronica Quantum, which installed the systems. “Students make up about 90 percent of the McDonald’s workforce in Venezuela. They were frequently punching one another in to cover for exams or other school-related events.
“A card only verifies a card,” adds Casal. “We have used finger scanning for other applications, but we believe that hand geometry is more effective and produces fewer errors when there are larger employee populations. With hand geometry, a larger area is scanned than with finger scans and the template is updated after every scan so it remains current.”
Instead of filling out or punching timecards, employees simply place their hands on the HandPunch. It automatically takes a three-dimensional reading of the size and shape of the employee’s hand and verifies the user’s identity in less than one second.
“McDonald’s worldwide success has been built on being fast, convenient and affordable. These are the same key factors that have made our hand geometry readers the most widely used biometric in the industry. That’s why they choose hand geometry over other biometrics,” reports Bashar Masad, marketing manager for Ingersoll Rand Recognition Systems. “With major fast food retailers such as McDonald’s realizing such tremendous cost savings by using our HandPunches, others are soon to follow.”
Supervisors at each franchise using the HandPunch terminals authorize and verify employee time and overtime on a computer located at the store. The hours are then sent to a central payroll processing center via a telephone line. The supervisors themselves also use the HandPunch to clock in and out.
“Most supervisors at McDonald’s are promoted from within and many find it difficult to impose rules and restrictions on their fellow workers,” Casal explains. “The HandPunch ensures that everyone is treated the same and fairly. McDonald’s employees are satisfied with the HandPunches because their payroll information is processed quickly and without mistakes. They receive regular reports with information about their time and attendance.”
Language is not an issue because the software is in Spanish and the HandPunch readers accommodate several languages.
About the Author
Tim O'Leary
Tim O'Leary is a security consultant, trainer and technician who has also been writing articles on all areas of locksmithing & physical security for many years.